Latest Posts
Understanding EDR Telemetry: Virtual Disk Mount
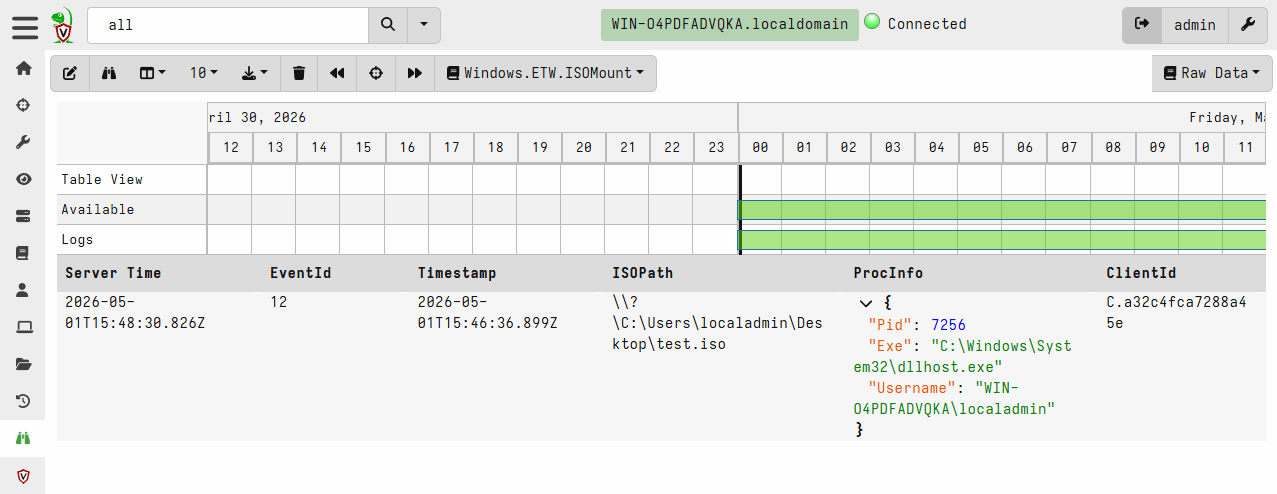
In 2022 Microsoft announced auto-blocking of macros in Office documents downloaded from the Internet, a popular initial access method for threat actors. This forced threat actors to turn to other less common methods of malware delivery. One of the methods that quickly gained traction was distribution through ISO-mounted files.
User double-clicks the ISO file, mounting it as a CD-ROM drive. The mounted drive contains a lure commonly in form of a LNK file masquerading as a document. When the victim executes the LNK lure it executes (often while utilizing additional tricks such as DLL-sideloading) a payload that is also placed on the mounted ISO drive. The payload and any other files except the lure file have hidden attribute set to avoid raising suspicion.
Read more →